Chinese Hackers Using New Manjusaka Hacking Framework to attack - Chinese sibling of Sliver and Cobalt Strike
8 August 2022
SafeAeon Inc.Researchers have disclosed a new hacking framework called Manjusaka that they call a "Chinese sibling of Sliver and Cobalt Strike."
The attack framework is identified as an imitation of the Cobalt Strike framework. The experts reported that Rust language for Windows and Linux is used to write the implants for the new malware family.
“A fully functional version of the command and control (C2), written in GoLang with a User Interface in Simplified Chinese, is freely available to download and can generate new implants with custom configurations with ease, thus, increasing the likelihood of wider adoption of this framework by malicious actors." reads the analysis published by Cisco Talos. “We have observed the same threat actor using the Cobalt Strike beacon and implants from the Manjusaka framework."
Researchers uncovered various campaigns leveraging phishing attempts via various documents themed around COVID-19 pandemic, the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. The documents were weaponized to kickstart the infection process and initiate the installation of the Cobalt Strike beacons on the infected systems.
Just like the Silver and Cobal Strike tools, the researchers believe that the Manjusaka tool also has the potential to become a popular post-exploitation tool.
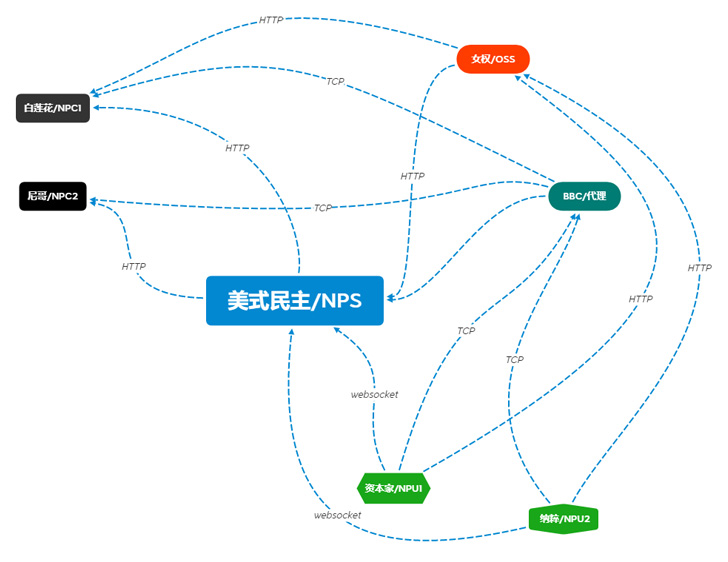
The researchers state that malware implant belongs to a RAT family called "Manjusaka." GoLang is used to write the C2 as an ELF binary and is available on GitHub at "[hxxps://github[.]com/YDHCUI/manjusaka]." Gin Web Framework is used to build the C2 server and admin panel. This framework allows operators to issue Rust-based implants/stagers commands on the compromised hosts. The implants support multiple capabilities listed below, including executing arbitrary codes and commands on the infected systems. The experts discovered both EXE and ELF versions of the implant.
Below is the complete list of Manjusaka Hacking Framework features:
- Execute arbitrary commands
- Retrieve various file statistics and information for any specific file
- Collect browser credentials from all popular, widely used web browsers, including Google Chrome, Microsoft Edge, Opera, and various other browsers.
- Collect Wi-Fi SSID and stored passwords
- Obtain Premiumsoft Navicat credentials
- Take screenshots of the current desktop and open windows
- Retrieve comprehensive system information from the infected endpoint
- Remotely leverage the file management modules to carry out various file-related activities
The attribution of this campaign to Chinese threat actors is based on the following evidence:
- The Rust-based implant does not use the standard crates.io library repository for dependency resolving. Instead, it was manually configured by the developers to use the mirror based out of the University Science and Technology of China (ustc[.]edu[.]cn).
- The maldoc refers to a COVID-19 outbreak specific to Golmud City.
- Simplified Chinese is used to write all the C2 menus and options.
- Researchers OSINT suggests that the author of this framework is in the Guangdong region of China.














